"The never normal" Acronis - Arsenal FC - Loughborough University
Accxia, Acronis, Arsenal FC, and Loughborough University presented "How to prepare for the never normal" at the prestigious Homehouse venue in...
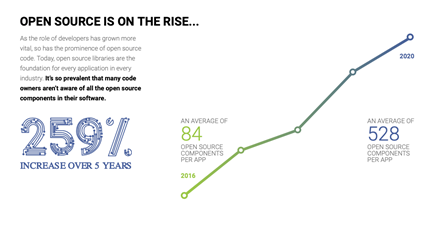
There’s no denying the value of open source software – and the growth of adoption underscores this.
Source: Synopsis, Inc.
In its 2021 report on open source security and risk, Synopsys, Inc. reported that of the over 1500 codebases it audited in 2020, 98% contained at least some open source code, and 75% were entirely open source.
Certainly, a big part of its attraction is the price, and in the case of offerings such as those provided by Atlassian users have access to a coherent and managed ecosystem of products.
But as with all software, responsible managers know there is a need for consistent attention to ensure the integrity of their IT domain. This is a cost regardless of whether it is open or proprietary.
Which brings us to some of the other Synopsis audit findings. It found that 84% of the open source codebases had at least one vulnerability – and the average number per codebase was far higher. Not all vulnerabilities are critical of course, but they classified 60% of those vulnerabilities as high risk. And the vulnerability picture for 2020 was worse than for the year before. In part this may be due to the fact that on average the vulnerabilities found were over 2 years old.
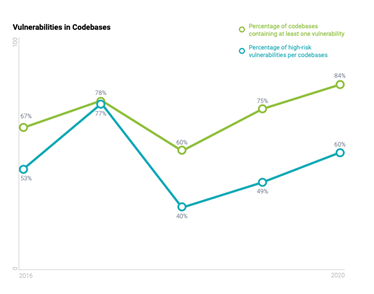
Source: Synopsis, Inc.
We know that all software is susceptible to vulnerabilities, and these can arise from any number of possible sources. That is true of proprietary and open source software alike, but in the case of open source, because there is no single vendor commercial license revenues to protect. This makes it all the more important for managers to take a disciplined and consistent approach to ensuring the integrity their software assets, and service providers such as Accxia are here to help.
You can download the full detail of the Synopsis, Inc. report here: https://www.synopsys.com/software-integrity/resources/analyst-reports/open-source-security-risk-analysis.html?intcmp=sig-mosaic-ossra21)
Kontaktieren Sie uns:

Accxia, Acronis, Arsenal FC, and Loughborough University presented "How to prepare for the never normal" at the prestigious Homehouse venue in...

Accxia has been approached by WebBeds, the European answer to Airbnb, to merge various Jira and Confluence instances following a couple of business...